Documentation Index
Fetch the complete documentation index at: https://core.vanish.trade/llms.txt
Use this file to discover all available pages before exploring further.

Turnkey Secure Enclaves
Vanish’s signing infrastructure is powered by Turnkey - wallet infrastructure built on hardware Trusted Execution Environments (TEEs). Private material is never stored unencrypted and is never exposed to Vanish, Turnkey, or any external process. Turnkey’s enclaves are highly constrained compute environments that can cryptographically attest to the code running inside. They are designed with:- No persistent storage
- No interactive access
- No external networking
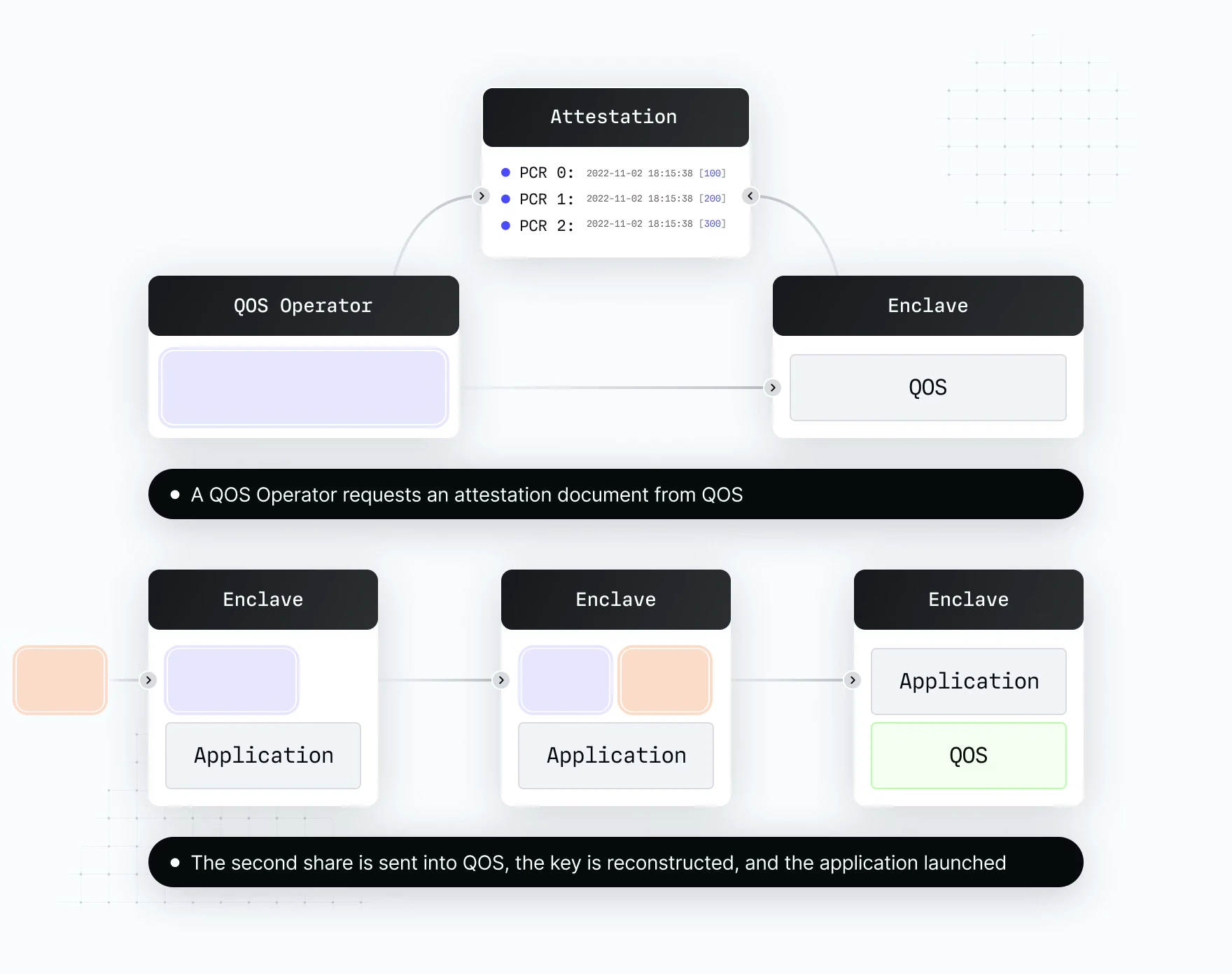
QuorumOS & Remote Attestation
Turnkey’s enclave stack runs QuorumOS - a minimal, immutable Linux unikernel designed for high-security environments with:- A deterministic build system for reproducible, auditable artifacts
- An initialization and attestation framework ensuring only authorised code runs inside the enclave
- No mutable state, no interactive shell, no external access surface
What This Means for Vanish Users
- Vanish never holds user private keys. All signing happens inside the enclave, initiated only by the user’s authenticated request.
- No human approval in the loop. All processes are fully automated - neither Vanish nor Turnkey can initiate or approve a transaction on behalf of a user.
- Integrating Vanish introduces no additional custodial risk to your platform or your users.
- Audited by Halborn. An independent security audit of Vanish’s infrastructure was conducted by Halborn, one of the leading blockchain security firms, trusted by Solana, Avalanche, and Coinbase.
- Operational security by Groom Lake. Staffed by NSA and CIA veterans, Groom Lake provides live threat monitoring, penetration testing, incident response, and global intelligence support.
Learn more: Turnkey security model · Halborn · Groom Lake